Browser Comparison - Mozilla Firefox Vs Internet Explorer
I had actually just recently paid $5 for SendMail service which allows my blog visitors to send me email through the contact form supplied in my blog site. Well, it is just a one-time cost and I think it definitely worth the price.
Check the stats of the programs that run daily in you "Task Supervisor" files - of your computer. Simply the other day I was establishing some cool artwork in photoshop. I decided to inspect my email, and examine my work concept. I pulled up my web browser to find that my internet browser was moving extremely sluggish. I discovered that photo shop was essentially using all of my CPU use- in photoshop, however soon as I closed Photoshop and my computer began to run much faster.
Attempt to stabilize paranoia with good sense. Some individuals get actually odd about infections, spyware, etc. It's just a computer! Back up your information and follow these actions, and it shouldn't be a huge issue.
Marketing On The Cheap - 7 Things You Can Learn From Offline Marketers
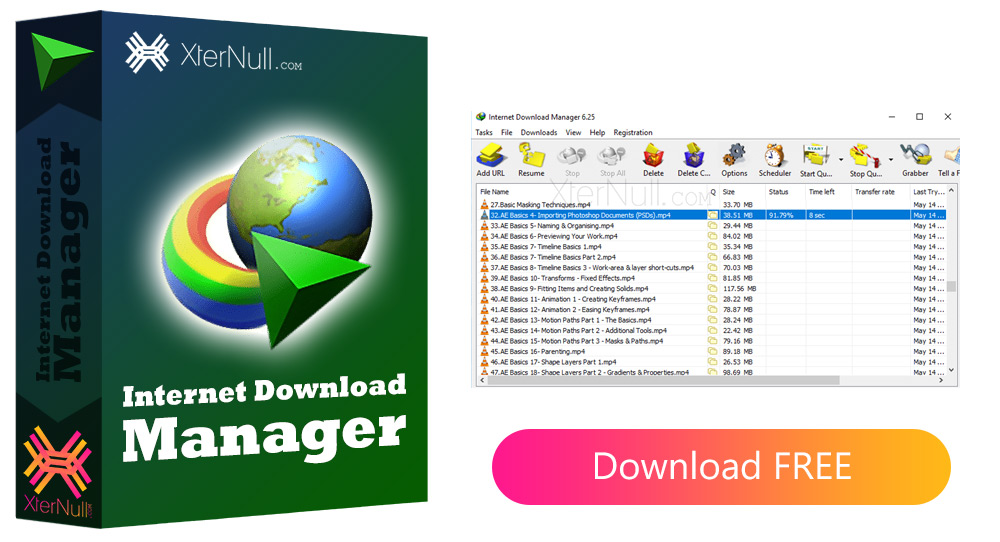
Mozilla is among the most popular names in Open Source software come Internet Download Manager a complete suite of totally freesoftware application such as Thunderbird (e-mail customer), Firefox (browser) and Sunbird (calendaring. Being open-source-based, there are many extensions and plug-ins you can discover to allow you to customize your programs.
A clienthad forgotten to bring their DVD video (in the old days it was VHS) to the exhibition. As an outcome, the exhibitionbooth had gorgeousdisplays that we had actuallydesigned IDM serial into cubicle walls that were turned off for the entireshow. These expensivetools that were supposed to be showing the customer's brand name video could not be utilized, as the customer did not have anything to be displayed on the monitors in the video's place.
There are many Web Security tools available in the market. Some of them are impressive. But still, none is best. It can't be. The very best protection is in your own hands. Follow a disciplined method while using Internet services.
A) A thumbdrive or a USB devicetakes upvery little IDM activation code room and can be indispensable if there is a need to make an extra copy of the video while on the roadway.
You offer hand-made knitted headscarfs. You can position your ad straight in the course of individuals looking for one. With some elbow grease and a sharp pencil you can determine to the cent what you can pay for to pay for that ad. And you can target the world or Little Rock Arkansas with that ad thanks to the awesome interface and techno-wizardry of Google Adwords. What pre-owned to take 3 months in the "old days" of marketing back in the nineties takes 3 hours today!
Click on the Start menu and search to C:\\ drive from My Computer system. Search for the Trojan infection' file using Windows Search. Type the name of the virus file in the desired field and hit Enter. When the file appears in the search results page, right click on it and choose Rename to change its name to something like virus_temp (you can call it anything you desire). The renaming will deteriorate the Trojan virus. Now best click on virus_temp and choose Delete to erase the file. Repeat the treatment for all the infected files.
